使用非root用户启动Rsyslog服务的的两种方法
1 使用systemctl模式启动ryslog服务[非root用户]
1.1 允许非root用户使用1024以下端口
linux允许非root用户默认只能使用1024以上端口,sysctl 可以修改该起始端口。
例:允许非root用户使用所有端口
#临时生效
sysctl net.ipv4.ip_unprivileged_port_start=0
#永久生效,需要重启系统
echo "net.ipv4.ip_unprivileged_port_start=0" >> /etc/sysctl.conf
1.2 编辑rsyslog服务端rsyslog.conf配置文件,添加启动用户配置参数
可以利用$PrivDropToUser、$PrivDropToUserID、$PrivDropToGroup和$PrivDropToGroupID配置指令以非root用户身份运行rsyslog。
使用这些变量时,rsyslog将以root身份启动,但在初始化完成后将下降到指定的用户或组。
然后,守护程序将根据指定用户或组的权限运行。
[rsyslog@syslog-server ]$ id
uid=1000(rsyslog) gid=1000(rsyslog) groups=1000(rsyslog),190(systemd-journal)
编辑/etc/rsyslog.conf配置文件添加以下配置
# 设置rsyslog 守护进程运行用户
# 1000为用户uid和gid
$PrivDropToUserID 1000
$PrivDropToGroupID 1000
1.3 修改systemctl rsyslog服务启动用户
在 CentOS/RHEL 7 中,rsyslog 默认以 root 身份运行,以非 root 用户身份运行时会出现权限问题。
要确保您可以从/run/logs/journal中的systemd日志中获取日志记录,请将指定的用户修改为"systemd-journald"组的成员:
# usermod -G systemd-journal [specified_user]
] usermod -G systemd-journal rsyslog
1.4 使用rsyslog用户重启rsyslog服务
[rsyslog@syslog-server ]$ systemctl restart rsyslog
1.5 修改/var目录下的log文件权限
让rsyslog用户有写的权限。
[root@rsyslog-server rsyslog]# chmod 722 /var/lib/rsyslog
[root@rsyslog-server rsyslog]# chmod 722 /var/log/messages
[root@rsyslog-server rsyslog]# chmod 722 /var/log/secure
[root@rsyslog-server rsyslog]# chmod 722 /var/log/maillog
[root@rsyslog-server rsyslog]# chmod 722 /var/log/cron
[root@rsyslog-server rsyslog]# chmod 722 /var/log/spooler
[root@rsyslog-server rsyslog]# chmod 722 /var/log/boot.lo
1.6 修改/var/lib/rsyslog目录权限
这一步很重要
含义:让rsyslog用户能读取imjournal.state文件。
[root@rsyslog-server rsyslog]# chmod -R 722 /var/lib/rsyslog
原权限为:
[root@rsyslog-server rsyslog]# ll /var/lib
drwx------. 2 root root 29 Mar 8 04:11 rsyslog
1.7 验证日志接收
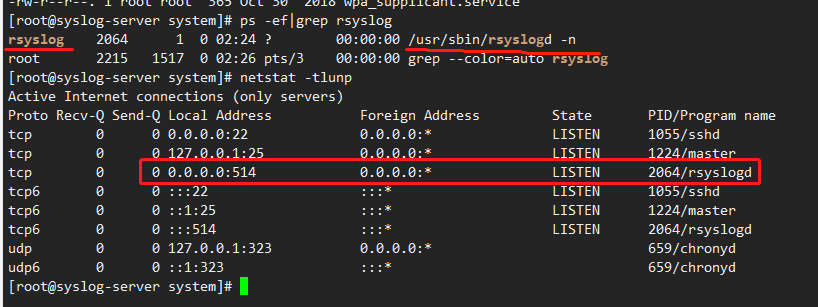
日志文件存在:
1.8 注意点
将rsyslog tls 密钥文件保存到/home/rsyslog目录中,或者让rsyslog用户有读取密钥文件的权限。
rsyslog数据保存路径,rsyslog用户需要有写的权限。
1.9 参考配置文件
# rsyslog configuration file
# For more information see /usr/share/doc/rsyslog-*/rsyslog_conf.html
# If you experience problems, see http://www.rsyslog.com/doc/troubleshoot.html
#### MODULES ####
# The imjournal module bellow is now used as a message source instead of imuxsock.
$ModLoad imuxsock # provides support for local system logging (e.g. via logger command)
$ModLoad imjournal # provides access to the systemd journal
#$ModLoad imklog # reads kernel messages (the same are read from journald)
#$ModLoad immark # provides --MARK-- message capability
# Provides UDP syslog reception
#$ModLoad imudp
#$UDPServerRun 514
# Provides TCP syslog reception
#$ModLoad imtcp
#$InputTCPServerRun 514
#### GLOBAL DIRECTIVES ####
# Where to place auxiliary files
$WorkDirectory /var/lib/rsyslog
# Use default timestamp format
$ActionFileDefaultTemplate RSYSLOG_TraditionalFileFormat
# File syncing capability is disabled by default. This feature is usually not required,
# not useful and an extreme performance hit
#$ActionFileEnableSync on
# Include all config files in /etc/rsyslog.d/
$IncludeConfig /etc/rsyslog.d/*.conf
# Turn off message reception via local log socket;
# local messages are retrieved through imjournal now.
$OmitLocalLogging on
# File to store the position in the journal
$IMJournalStateFile imjournal.state
#### RULES ####
# Log all kernel messages to the console.
# Logging much else clutters up the screen.
#kern.* /dev/console
# Log anything (except mail) of level info or higher.
# Don't log private authentication messages!
*.info;mail.none;authpriv.none;cron.none /var/log/messages
# The authpriv file has restricted access.
authpriv.* /var/log/secure
# Log all the mail messages in one place.
mail.* -/var/log/maillog
# Log cron stuff
cron.* /var/log/cron
# Everybody gets emergency messages
*.emerg :omusrmsg:*
# Save news errors of level crit and higher in a special file.
uucp,news.crit /var/log/spooler
# Save boot messages also to boot.log
local7.* /var/log/boot.log
# ### begin forwarding rule ###
# The statement between the begin ... end define a SINGLE forwarding
# rule. They belong together, do NOT split them. If you create multiple
# forwarding rules, duplicate the whole block!
# Remote Logging (we use TCP for reliable delivery)
#
# An on-disk queue is created for this action. If the remote host is
# down, messages are spooled to disk and sent when it is up again.
#$ActionQueueFileName fwdRule1 # unique name prefix for spool files
#$ActionQueueMaxDiskSpace 1g # 1gb space limit (use as much as possible)
#$ActionQueueSaveOnShutdown on # save messages to disk on shutdown
#$ActionQueueType LinkedList # run asynchronously
#$ActionResumeRetryCount -1 # infinite retries if host is down
# remote host is: name/ip:port, e.g. 192.168.0.1:514, port optional
#*.* @@remote-host:514
# ### end of the forwarding rule ###
$PrivDropToUserID 1000
$PrivDropToGroupID 1000
# $ModLoad imuxsock # local messages
# imuxsock配置不能存在多次。。。
$ModLoad imtcp # TCP listener
$DefaultNetstreamDriver gtls # 默认为GTLS驱动程序,make gtls driver the default
$DefaultNetstreamDriverCAFile /home/rsyslog/pem/ca.pem # certificate files CA 密钥
$DefaultNetstreamDriverCertFile /home/rsyslog/pem/machine-cert.pem # 客户端证书
$DefaultNetstreamDriverKeyFile /home/rsyslog/pem/machine-key.pem # 客户端私钥
$InputTCPServerStreamDriverAuthMode anon # 驱动程序认证模式
$InputTCPServerStreamDriverMode 1 # 在tls模式下运行驱动程序
$InputTCPServerRun 514 # 在1514端口启动监听器,接收发送到tcp/1514端口上的数据
$template Remote,"/home/syslog/%fromhost-ip%/%$YEAR%-%$MONTH%-%$DAY%.log" ## 数据保存策略
:fromhost-ip, !isequal, "127.0.0.1" ?Remote
& ~
2 使用command模式启动rsyslog服务[非root用户]
2.1 创建rsyslog用户
创建rsyslog用户,并设置密码,必须步骤
~ ] useradd rsyslog
~ ] password rsyslog
~ ] id rsyslog
uid=1002(rsyslog) gid=1002(rsyslog) groups=1002(rsyslog)
2.2 将rsyslog.conf和rsyslog TLS证书保存到rsyslog家目录中
将rsyslog.conf、rsyslog TLS证书全部保存到/home/rsyslog目录中
rsyslogd.conf 配置文件内容如下
# rsyslog configuration file # For more information see /usr/share/doc/rsyslog-*/rsyslog_conf.html # If you experience problems, see http://www.rsyslog.com/doc/troubleshoot.html #### MODULES #### # The imjournal module bellow is now used as a message source instead of imuxsock. $ModLoad imuxsock # provides support for local system logging (e.g. via logger command) $ModLoad imjournal # provides access to the systemd journal #$ModLoad imklog # reads kernel messages (the same are read from journald) #$ModLoad immark # provides --MARK-- message capability # Provides UDP syslog reception # $ModLoad imudp # $UDPServerRun 514 # Provides TCP syslog reception #$ModLoad imtcp #$InputTCPServerRun 514 #### GLOBAL DIRECTIVES #### # Where to place auxiliary files $WorkDirectory /var/lib/rsyslog # Use default timestamp format $ActionFileDefaultTemplate RSYSLOG_TraditionalFileFormat # File syncing capability is disabled by default. This feature is usually not required, # not useful and an extreme performance hit #$ActionFileEnableSync on # Include all config files in /etc/rsyslog.d/ $IncludeConfig /etc/rsyslog.d/*.conf # Turn off message reception via local log socket; # local messages are retrieved through imjournal now. $OmitLocalLogging on # File to store the position in the journal $IMJournalStateFile imjournal.state #### RULES #### # Log all kernel messages to the console. # Logging much else clutters up the screen. #kern.* /dev/console # Log anything (except mail) of level info or higher. # Don't log private authentication messages! # *.info;mail.none;authpriv.none;cron.none /var/log/messages # The authpriv file has restricted access. authpriv.* /var/log/secure # Log all the mail messages in one place. mail.* -/var/log/maillog # Log cron stuff cron.* /var/log/cron # Everybody gets emergency messages *.emerg :omusrmsg:* # Save news errors of level crit and higher in a special file. uucp,news.crit /var/log/spooler # Save boot messages also to boot.log local7.* /var/log/boot.log # ### begin forwarding rule ### # The statement between the begin ... end define a SINGLE forwarding # rule. They belong together, do NOT split them. If you create multiple # forwarding rules, duplicate the whole block! # Remote Logging (we use TCP for reliable delivery) # # An on-disk queue is created for this action. If the remote host is # down, messages are spooled to disk and sent when it is up again. #$ActionQueueFileName fwdRule1 # unique name prefix for spool files #$ActionQueueMaxDiskSpace 1g # 1gb space limit (use as much as possible) #$ActionQueueSaveOnShutdown on # save messages to disk on shutdown #$ActionQueueType LinkedList # run asynchronously #$ActionResumeRetryCount -1 # infinite retries if host is down # remote host is: name/ip:port, e.g. 192.168.0.1:514, port optional #*.* @@remote-host:514 # TCP/SSL Test # $ModLoad imuxsock # local messages $ModLoad imtcp # TCP listener # $PrivDropToGroup rsyslog # $PrivDropToUser rsyslog # make gtls driver the default $DefaultNetstreamDriver gtls # certificate files # $DefaultNetstreamDriverCAFile /opt/pem/ca.pem # $DefaultNetstreamDriverCertFile /opt/pem/machine-cert.pem # $DefaultNetstreamDriverKeyFile /opt/pem/machine-key.pem $DefaultNetstreamDriverCAFile /home/rsyslog/tls/myCert.pem $DefaultNetstreamDriverCertFile /home/rsyslog/tls/myCert.pem $DefaultNetstreamDriverKeyFile /home/rsyslog/tls/myKey.key $InputTCPServerStreamDriverAuthMode anon $InputTCPServerStreamDriverMode 1 # run driver in TLS-only mode $InputTCPServerRun 514 # start up listener at port 1514 # 保存syslog file path # $template Remote,"/var/log/syslog/%fromhost-ip%/%$YEAR%-%$MONTH%-%$DAY%.log" # $template ipRemote,"/var/log/syslog/%FROMHOST-IP%/%$YEAR%-%$MONTH%-%$DAY%.log" # if $fromhost-ip == '10.10.0.100' then ?ipRemote # & ~ $template Remote,"/home/rsyslog/%fromhost-ip%/%$YEAR%-%$MONTH%-%$DAY%.log" :fromhost-ip, !isequal, "127.0.0.1" ?Remote & ~ # ### end of the forwarding rule ###证书保存情况:
[rsyslog@linux-syslogserver ~]$ pwd /home/rsyslog [rsyslog@linux-syslogserver ~]$ ll total 16 drwx------. 2 rsyslog rsyslog 28 May 4 06:27 10.10.0.100 -rw-rw-r--. 1 rsyslog rsyslog 4 May 4 06:58 log.pid -rw-------. 1 rsyslog rsyslog 262 May 4 06:55 nohup.out -rw-r--r--. 1 rsyslog rsyslog 4498 May 4 06:57 rsyslog.conf drwx------. 2 rsyslog rsyslog 41 May 4 05:54 tls
2.3 指定/usr/sbin/rsyslogd能使用1024以下端口
指定/usr/sbin/rsyslogd程序能使用1024以下端口
~ ] setcap cap_net_bind_service=+eip /usr/sbin/rsyslogd
补充:取消程序使用1024以下端口(不要执行)~ ] setcap -r /path/to/application
2.4 修改/var目录下的log文件权限
让rsyslog用户有写的权限。
[root@rsyslog-server rsyslog]# chmod 722 /var/lib/rsyslog
[root@rsyslog-server rsyslog]# chmod 722 /var/log/messages
[root@rsyslog-server rsyslog]# chmod 722 /var/log/secure
[root@rsyslog-server rsyslog]# chmod 722 /var/log/maillog
[root@rsyslog-server rsyslog]# chmod 722 /var/log/cron
[root@rsyslog-server rsyslog]# chmod 722 /var/log/spooler
[root@rsyslog-server rsyslog]# chmod 722 /var/log/boot.lo
2.5 修改/var/lib/rsyslog目录权限
这一步很重要含义:让rsyslog用户能读取imjournal.state文件。
[root@rsyslog-server rsyslog]# chmod -R 722 /var/lib/rsyslog # 原权限为: [root@rsyslog-server rsyslog]# ll /var/lib drwx------. 2 root root 29 Mar 8 04:11 rsyslog # 更改后权限为: [root@rsyslog-server rsyslog]# ll /var/lib drwx-w--w-. 2 root root 29 Mar 8 04:11 rsyslog
2.6 使用命令行启动rsyslogd程序
~ ] $ nohup /usr/sbin/rsyslogd -n -f /home/rsyslog/rsyslog.conf -i /home/rsyslog/log.pid >/dev/null 2>&1 &
[1] 2764
~ ] $
2.7 配置检查
# 检查端口 514端口是否启动
[root@linux-syslogserver 10.10.0.100]# netstat -tlunp
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:514 0.0.0.0:* LISTEN 2764/rsyslogd
tcp 0 0 127.0.0.1:38091 0.0.0.0:* LISTEN 1288/node
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 942/sshd
tcp 0 0 127.0.0.1:25 0.0.0.0:* LISTEN 1103/master
tcp6 0 0 :::514 :::* LISTEN 2764/rsyslogd
tcp6 0 0 :::8080 :::* LISTEN 943/httpd
tcp6 0 0 :::22 :::* LISTEN 942/sshd
tcp6 0 0 ::1:25 :::* LISTEN 1103/master
udp 0 0 127.0.0.1:323 0.0.0.0:* 717/chronyd
udp6 0 0 ::1:323 :::* 717/chronyd
# 检查日志文件是否更新
[rsyslog@linux-syslogserver ~]$ tail -f /home/rsyslog/10.10.0.100/2023-05-04.log
May 4 18:59:03 other-server root: rsyslog test aaaaaaaaaaaabbbbbbbbbbbbbCCCCCCCCCCCCCCCCCCCCCCCb
May 4 19:01:01 other-server crond[7595]: pam_limits(crond:session): invalid line 'End of file' - skipped
May 4 19:01:01 other-server systemd: Started Session 4 of user root.
May 4 19:01:01 other-server CROND[7597]: (root) CMD (run-parts /etc/cron.hourly)
May 4 19:01:01 other-server run-parts(/etc/cron.hourly)[7597 starting 0anacron
May 4 19:01:01 other-server run-parts(/etc/cron.hourly)[7606 finished 0anacron
May 4 19:08:54 other-server chronyd[774]: Selected source 119.28.206.193
May 4 19:09:01 other-server anacron[3878]: Job `cron.weekly' started
May 4 19:09:01 other-server anacron[3878]: Job `cron.weekly' terminated
May 4 19:09:01 other-server anacron[3878]: Normal exit (2 jobs run)


-d2979772834f4346a961b123d2a49447.jpg)

评论区